Effortless password audits
Passwords. They are the keys to our digital kingdoms. And these days most organisations will have security controls in place, such as 2 Factor Authentication, to complement the traditional password and help prevent credential stuffing attacks. (sidenote: did you know that 2FA deployed on your Exchange server can be effortlessly bypassed?)
But that doesn’t mean we can lax the rules around passwords. They still play a huge part in protecting our data. According to the Verizon 2017 Data Breach Investigations Report 81% of hacking-related data breaches involve leveraging stolen and/or weak passwords.
And yet I see time and time again organisations enabling “complex” password composition rules and be done with it. But these rules don’t go far enough. Passwords such as Passw0rd, London18 and Qwerty123 would meet most organisations complexity requirements, and would be amongst the first attempted in a brute-force attack. When conducting security audits I still regularly see passwords containing the company name or office address, i.e. Acme2018 or 17StationRoad.
This is why you should be auditing your passwords. They can provide invaluable insight into understanding the security awareness levels of your staff. A large number of users with weak and predictable passwords can suggest cultural issues, inadequate training, and even identify staff with low levels of engagement — something you can begin to fix.
Effortless audits
The cracking process of a password audit is always going to be the largest limiting factor in terms of time. You don’t need to crack all passwords - just the weak ones - and sometimes cracking on your local machine is sufficient enough. For larger organisations, it’s easy enough to spin up an Amazon’s AWS GPU instance. The p2.16xlarge with 16 GPUs, for example, can work through 130702 MILLION PASSWORDS PER SECOND. Even then it can take a few days to crack upwards of 90%.
You then need to analyse the passwords and determine if they are good or bad. And who wants to manually analyse 1000s of passwords, pick out interesting statistics and create various reports?
To make this process less painful, I have developed a tool called cracke-dit (“Cracked It”) – free and open-source for all – that directly extracts passwords from a Windows Domain Controller, analyse them, and output the data in various different formats.

And you can produce funky things such as a password cloud:
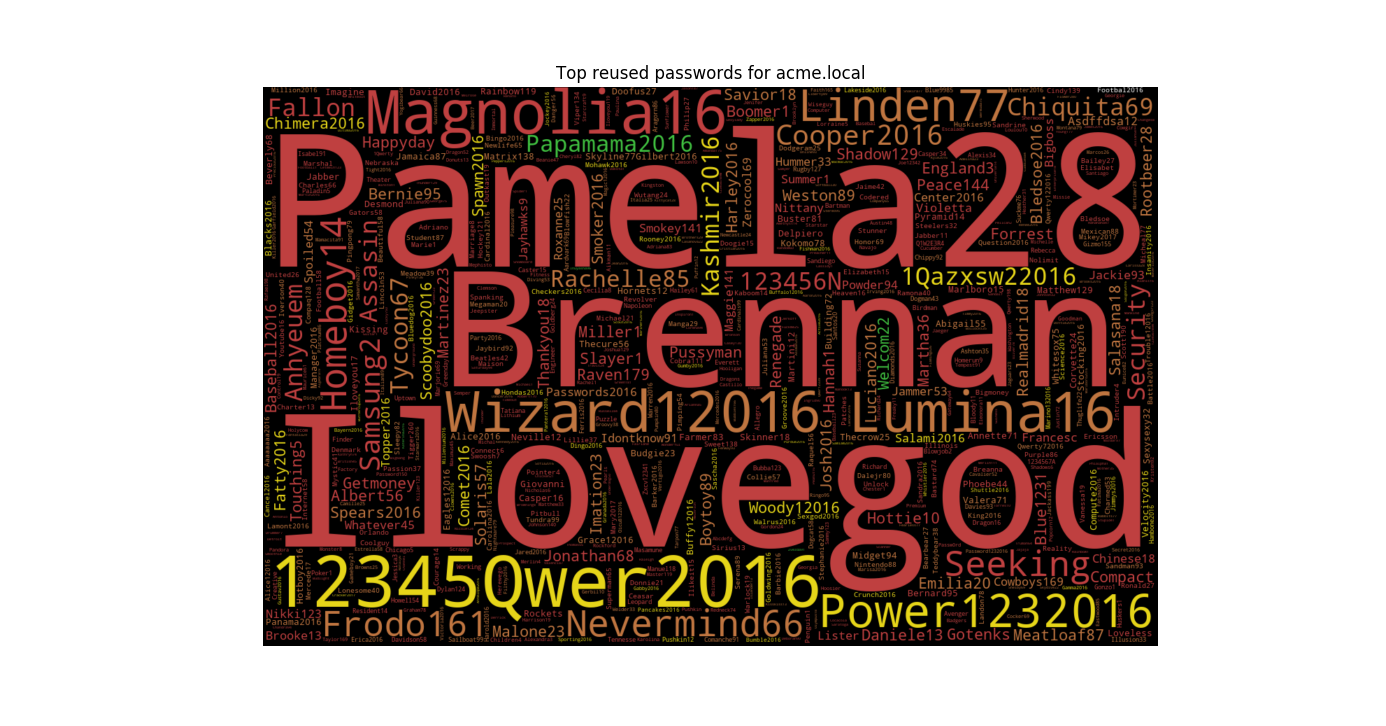
Passwords are scored based on complexity using Dropbox’s zxcvbn algorithm, where 0 is a bad password and 4 is a good password. To get an idea on how unique users passwords are, they are also checked against Have I Been Pwned, using k-Anonymity to ensure passwords are kept secure.
You can then begin to develop training programmes to improve your staff’s password hygiene and general security awareness.
Securing passwords
One of the golden rules I’ve learned from my programming background is to never trust user input. The same applies to passwords and you should plan for them to be compromised at some point. Here are 5 things you should be doing:
-
Ensure wherever a password is used externally, it has adequate security controls in place such as rate limiting and 2 Factor Authentication. Take into account other factors such as login time, geographical location, and IP address and deny login attempts if it falls outside of the user’s usual pattern.
-
Teach your users what a good password looks like (hint: a long pass phrase). Why is it important? Show examples of good and bad passwords. Make sure this advice is embedded within your induction programme for new joiners.
-
Gradually increase the minimum password length requirement to a minimum of 10, ideally 12, characters. Longer passwords increase entropy, which means they are (generally) more secure. Consider rolling out a password manager and adequate training to help with this.
-
Audit passwords monthly (or at least quarterly) to identify training needs for users who are still struggling to create strong passwords. Reward staff who are creating better passwords.
-
Stop forcing users to reset their password every X days. Yes, it reduces risk but at great cost. Research suggests this leads to users creating weaker passwords over time. Only force users to reset passwords if you believe they have been compromised.